What is Reverse Proxy: Boosting Security, Speed, and Scalability in Modern Web Development
What is Reverse Proxy: Boosting Security, Speed, and Scalability in Modern Web Development
The increasing demand for online applications and services has created a complex web development landscape. As more businesses and organizations expand their online presence, websites and applications face numerous challenges in delivering fast, secure, and scalable services. One of the key solutions to these challenges lies in leveraging reverse proxy techniques, which enhance the performance, security, and robustness of online systems. This article delves into the essence of reverse proxy technology, its uses, benefits, and key features, providing valuable insights for web developers and IT professionals navigating the complex world of online applications.
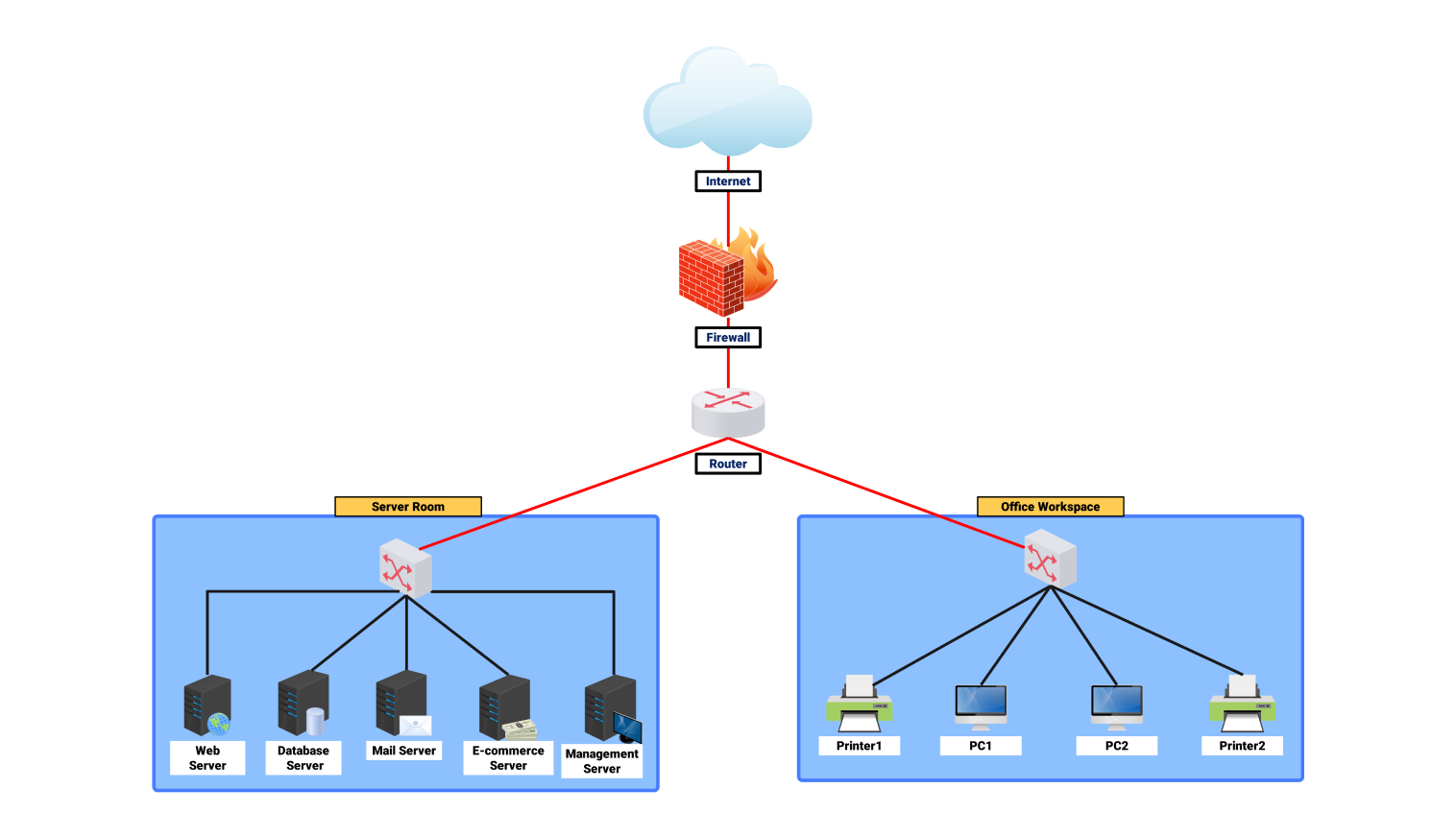
A reverse proxy acts as an intermediary entity between clients (users) and servers, accepting incoming HTTP requests and forwarding them to the actual destination server. By doing so, it can cache frequently-used resources, protect servers from direct web attacks, distribute traffic across multiple servers, and adapt to various workload levels. The technology allows developers to create scalable, secure, and high-performance applications that can withstand the demands of an ever-increasing online presence.
Key Benefits of Reverse Proxy Technology
Reverse proxy technology is often overlooked but underpins a significant portion of current online infrastructure. Besides providing an additional layer of security and reducing the workload on origin servers, reverse proxies also offer a number of critical advantages for websites and web services:
* **Improved load balancing**: By distributing traffic across multiple servers, reverse proxies ensure that origin servers are not overwhelmed by a large number of requests, enabling organizations to maintain a seamless user experience even in the face of high traffic.
* **Enhanced security**: By adding an additional layer between the client and the server, reverse proxies protect against common web attacks, such as SQL Injection, Cross-Site Scripting (XSS), and Denial of Service (DoS) attacks.
* **Content caching**: Frequently-used resources are cached at the proxy level, reducing the need for users to retrieve content from the origin server, thereby decreasing latency and improving the user experience.
* **Cookie handling**: Reverse proxies manage session cookies for users, simplifying the process of routing users to the correct servers and streamlining authentication processes.
* **Logging and analytics**: Many reverse proxy solutions, such as Squid and NGINX, come equipped with built-in logging functionality, allowing organizations to capture information about pages loaded, requests made, and various other aspects of website performance.
* **Spoofing protection**: Reverse proxy technology helps safeguard websites against spoofing attacks by ensuring that modifications to content source address is merged.
* **Content filtering**: Organizations can leverage reverse proxy servers to filter out malicious and harmful content.
Popular Types of Reverse Proxies
Reverse proxies are categorized into two primary categories:
* **Caching Proxies**: These can store content so frequently accessed that they do not require obtaining them from the server, reducing the load and enhancing overall user experience.
* **Proxy servers configured to specify caching of web pages**: Many proxy frameworks rely on advanced caching algorithms to store even less frequent requests, optimizing access to web pages.
Implementing Reverse Proxies in Modern Applications
Implementing a reverse proxy in your application involves setting up a forward facing server that sits just in front of the origin server. This forward facing server will interact with your client, handling requests, forwarding, and wrapping responses to present a more robust form of internet communication:
**1.** Load Balancing: Together, and in a complementary manner you mask servers behind a frontend handler so they don't crash.
**2.** Authentication Checks: Authursors manage [CA SSH Angular keys securely to make your user signup successful.


Related Post
:max_bytes(150000):strip_icc():focal(624x0:626x2)/Christmas-Storys-Peter-Billingsley-Talks-35-Years-of-Friendship-with-Vince-Vaughn-121523-2-3b030f04550a4d498c3b103dc7866ce8.jpg)
Peter Billingsley and Vince Vaughn: A Delightfully Dysfunctional Bromance For The Ages
Unveiling the Enigmatic Taelyn Leigh West: A Deep Dive into the Life and Career of a Rising Star

The Bigger Picture: Kanye West's New Lyrics Spark Outrage Among Fans

Unveiling the Mysterious World of the 28th Street Gang: A Story of Power, Corruption, and Resilience

