Unlocking the Secrets of Secure Communication: Public Key Cryptography Explained Simply
Unlocking the Secrets of Secure Communication: Public Key Cryptography Explained Simply
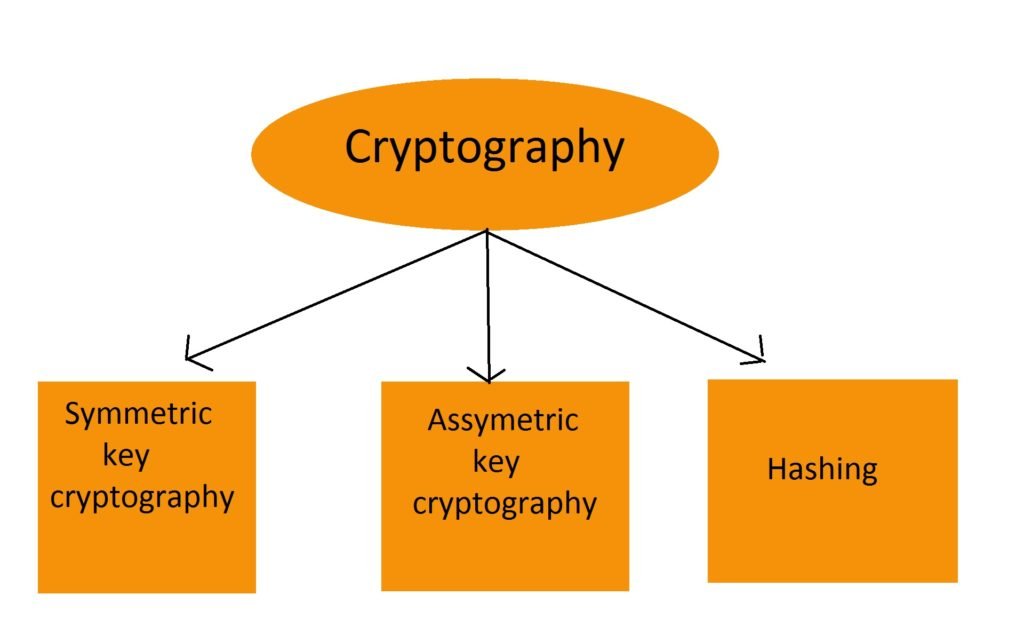
Public key cryptography has revolutionized the way we communicate and conduct transactions online, providing a secure means of encrypting and decrypting data. This cryptographic technique uses a pair of keys – a public key for encryption and a private key for decryption – to ensure that sensitive information remains confidential. In this article, we will delve into the world of public key cryptography, exploring its history, concepts, and applications, making it easier to understand the intricacies of this complex technology.
What is Public Key Cryptography?
Public key cryptography is a type of cryptographic technique that uses a pair of keys to encrypt and decrypt data. The public key is used to encrypt the data, while the private key is used to decrypt it. This means that anyone can use the public key to encrypt a message, but only the owner of the private key can decrypt it. This process ensures that the data remains confidential, even if it is intercepted during transmission.
The Basics of Public Key Cryptography
Public key cryptography is based on the concept of asymmetry, where the public key is used for encryption and the private key is used for decryption. The public key is derived from the private key using mathematical algorithms, such as RSA (Rivest-Shamir-Adleman) and elliptic curve cryptography. The RSA algorithm, for example, uses a pair of large prime numbers to generate a public key and a private key.
The public key is made up of two components: the modulus (n) and the exponent (e). The modulus (n) is the product of two large prime numbers, while the exponent (e) is a number between 1 and n-1. The private key is made up of the modulus (n) and the exponent (d), where d is the modular inverse of e modulo n.
How Public Key Cryptography Works
Here is a step-by-step explanation of how public key cryptography works:
1. **Key Generation**: A user generates a pair of keys, a public key and a private key, using a key generation algorithm.
2. **Encryption**: The user encrypts a message using the public key. This is done by taking the message and raising it to the power of the public key exponent (e), modulo the modulus (n).
3. **Transmission**: The encrypted message is transmitted over a public channel, such as the internet.
4. **Decryption**: The recipient receives the encrypted message and decrypts it using their private key. This is done by taking the encrypted message and raising it to the power of the private key exponent (d), modulo the modulus (n).
Real-World Applications of Public Key Cryptography
Public key cryptography has numerous real-world applications, including:
* **Secure Online Transactions**: Public key cryptography is used to secure online transactions, such as online banking and e-commerce. It ensures that sensitive information, such as credit card numbers and passwords, remains confidential.
* **Email Encryption**: Public key cryptography is used to encrypt and decrypt emails, ensuring that sensitive information remains confidential.
* **Secure Communication**: Public key cryptography is used to secure communication between parties, such as in the case of secure voice and video calls.
Examples of Public Key Cryptography in Use
Here are a few examples of public key cryptography in use:
* **Secure Web Browsing**: When you visit a website, your browser encrypts your communication using public key cryptography.
* **Online Banking**: Online banking platforms use public key cryptography to secure your transactions and ensure that your sensitive information remains confidential.
* **Email Encryption**: Email providers, such as ProtonMail and Tutanota, use public key cryptography to encrypt and decrypt emails.
Limitations of Public Key Cryptography
While public key cryptography is a powerful tool for securing communication and transactions, it has some limitations. Some of the limitations include:
* **Key Size**: Public key cryptography requires large key sizes, which can make it slow and computationally intensive.
* **Key Management**: Managing public and private keys can be complex and time-consuming.
* **Cryptanalysis**: Public key cryptography can be vulnerable to cryptanalysis, which is the practice of breaking the encryption algorithm.
Challenges and Future Developments
While public key cryptography has come a long way, there are still challenges and future developments to be explored. Some of the challenges and developments include:
* **Quantum Computing**: Quantum computers have the potential to break public key cryptography algorithms, such as RSA and elliptic curve cryptography.
* **Post-Quantum Cryptography**: Researchers are exploring new cryptographic techniques that are resistant to quantum computing, such as lattice-based cryptography and code-based cryptography.
* **Keyless Cryptography**: Researchers are exploring new cryptographic techniques that do not rely on key management, such as homomorphic encryption and multiparty computation.
Conclusion
In conclusion, public key cryptography is a powerful tool for securing communication and transactions online. It has numerous real-world applications, including secure online transactions, email encryption, and secure communication. While it has limitations, researchers are exploring new cryptographic techniques and addressing the challenges of key size, key management, and cryptanalysis. As the world becomes increasingly dependent on online communication and transactions, public key cryptography will play a crucial role in ensuring the security and confidentiality of sensitive information.



Related Post

Kenneth Washington Finally Reveals His Impressive Net Worth: You Won't Believe What It Takes To Be This Wealthy

Verify Your Future: The Importance of Pharmacy Technician License Verification in California

Collin County Jail Inmate Search: A Comprehensive Guide to Finding Information on Inmates
The Height of a Legend: Uncovering the True Height of Elvis Presley