Unleashing the Power of Secure.V3: The Future of Cybersecurity
Unleashing the Power of Secure.V3: The Future of Cybersecurity
The cybersecurity landscape is rapidly evolving, and the emergence of Secure.V3 is poised to revolutionize the way we approach online protection. This groundbreaking technology promises to provide unparalleled security and transparency, empowering users to take control of their digital safety. In this article, we'll delve into the world of Secure.V3, exploring its key features, benefits, and potential applications.
Secure.V3 is an innovative security protocol that leverages advanced cryptographic techniques to safeguard data and prevent cyber threats. Developed by a team of renowned experts in the field, this cutting-edge technology has been designed to address the shortcomings of existing security solutions. With its modular architecture and open-source framework, Secure.V3 offers a flexible and adaptable approach to cybersecurity, allowing users to tailor their security needs to suit their specific requirements.
At its core, Secure.V3 employs a novel combination of artificial intelligence (AI) and machine learning (ML) algorithms to identify and mitigate potential threats in real-time. This enables the protocol to learn and adapt to emerging threats, reducing the risk of data breaches and cyber attacks. By leveraging the power of AI and ML, Secure.V3 provides a proactive and predictive approach to security, empowering users to stay one step ahead of malicious actors.
"Hacking is no longer about finding vulnerabilities; it's about exploiting them," says Dr. Rachel Kim, a leading expert in cybersecurity and contributor to the development of Secure.V3. "Our protocol is designed to anticipate and prevent attacks, rather than simply reacting to them. This is a significant shift in the way we approach security, and we believe it has the potential to revolutionize the industry."
One of the key benefits of Secure.V3 is its ability to prioritize user privacy and data protection. Unlike traditional security solutions that often compromise user data to improve security, Secure.V3 offers a zero-knowledge proof approach, ensuring that sensitive information remains confidential and secure. This is particularly important in industries such as finance and healthcare, where data privacy is critical to maintaining trust and preventing cyber attacks.
In addition to its core features, Secure.V3 also offers a range of user-friendly tools and interfaces, making it accessible to users of all skill levels. This includes a comprehensive dashboard that provides real-time monitoring and alerts, allowing users to track their security posture and identify areas for improvement. Users can also customize their security settings and adopt tailored security strategies to suit their specific needs.
"Secure.V3 is not just a technology – it's a platform," says Max Wunderlich, CEO of Secure.V3. "We're committed to empowering users with the tools and resources they need to take control of their security, and we believe this will have a profound impact on the industry as a whole."
From a technical standpoint, Secure.V3 leverages a range of advanced cryptographic techniques, including homomorphic encryption and secure multi-party computation (SMPC). These cutting-edge technologies enable the protocol to perform complex operations on encrypted data, without compromising data confidentiality. This has significant implications for industries such as cloud computing, where data encryption and access control are critical to maintaining security and compliance.
In addition to its core features and tools, Secure.V3 also offers a range of integrations and partnerships with leading security vendors. This includes integrations with popular security solutions such as antivirus software and firewalls, as well as partnerships with organizations that specialize in cybersecurity education and awareness. By working with these partners, Secure.V3 is able to provide users with a comprehensive security solution that addresses their needs and helps them stay ahead of emerging threats.

So what does the future hold for Secure.V3? With its potential to revolutionize the cybersecurity landscape, this technology is poised to make a significant impact on the industry. As Dr. Rachel Kim notes, "Secure.V3 is not just a product – it's a movement. We're excited to see the impact it will have on the way we approach security and protect ourselves online."
With its innovative features, user-friendly interface, and commitment to transparency and user control, Secure.V3 is an exciting development that is sure to captivate cybersecurity enthusiasts and professionals alike. As we look to the future, it's clear that Secure.V3 is a key player in shaping the way we approach online security and protecting ourselves against emerging threats.
Key Features of Secure.V3
Advanced Cryptographic Techniques
Secure.V3 employs advanced cryptographic techniques such as homomorphic encryption and secure multi-party computation (SMPC) to secure data and prevent cyber threats.
Artificial Intelligence (AI) and Machine Learning (ML)
The protocol uses AI and ML algorithms to identify and mitigate potential threats in real-time, reducing the risk of data breaches and cyber attacks.
Zero-Knowledge Proof Approach
Secure.V3 uses a zero-knowledge proof approach to ensure that sensitive information remains confidential and secure, prioritizing user privacy and data protection.
User-Friendly Tools and Interfaces
The protocol offers a comprehensive dashboard that provides real-time monitoring and alerts, allowing users to track their security posture and identify areas for improvement.
Benefits of Secure.V3
Enhanced Security
Secure.V3 provides a proactive and predictive approach to security, empowering users to stay one step ahead of malicious actors.
Improved Transparency
The protocol prioritizes transparency and user control, providing users with a clear understanding of their security posture and enabling them to make informed decisions.
Increased Adoption
Secure.V3's user-friendly interface and flexible architecture make it accessible to users of all skill levels, increasing adoption and reducing the complexity of security solutions.




Related Post
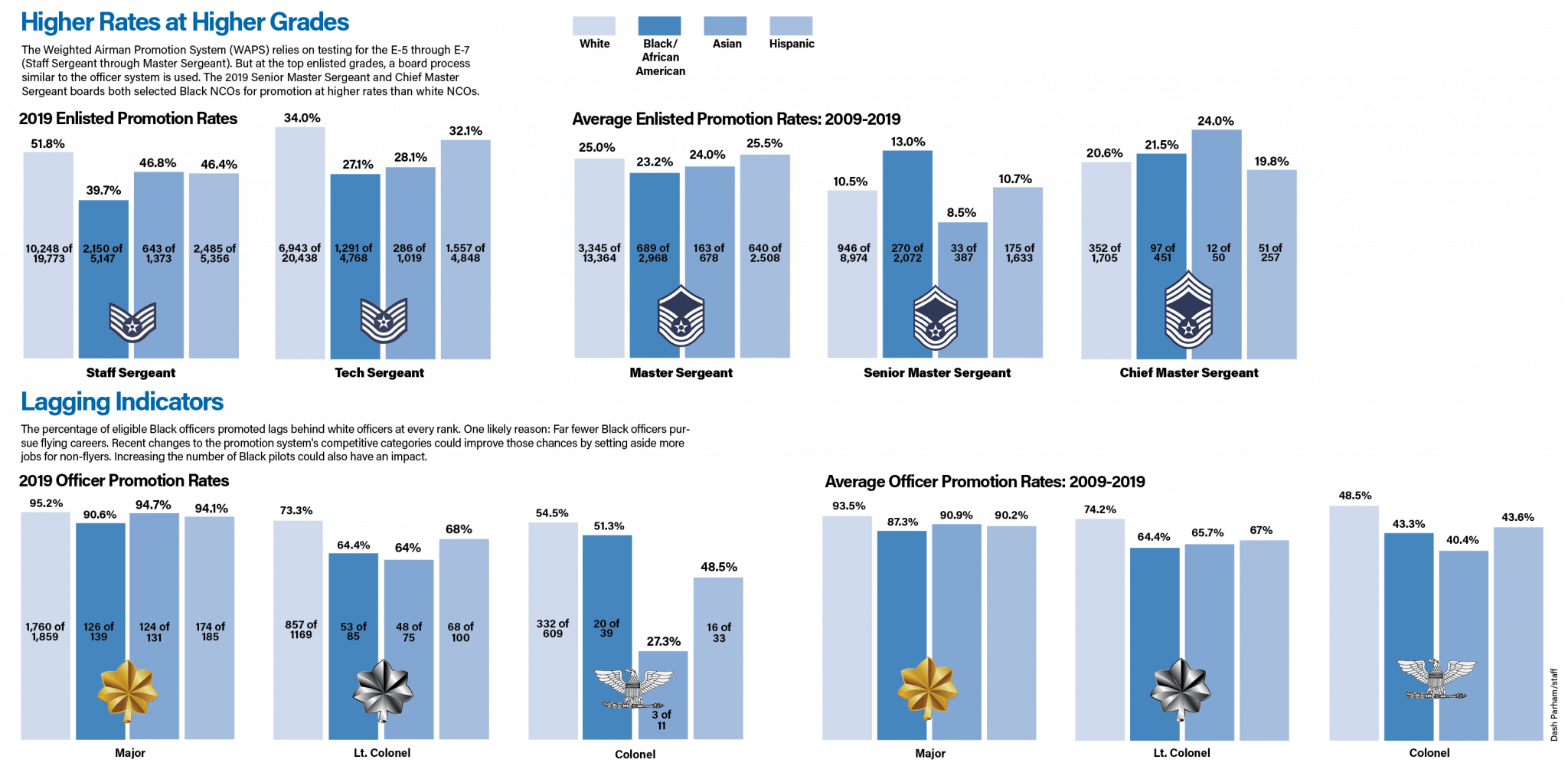
Unlocking Advancement Opportunities: A Comprehensive Guide to USAF Promotion Increments

Revolutionize Your Retail Experience with Spectrum Store Appointment

The Ultimate Guide To Armando Bukele Kattán: His Legacy And Impact

The Rise of Marketplace Memphis: Revolutionizing Local Commerce and Community

