The Rise of Cybersecurity Vulnerabilities: Why Data Breaches are on the Rise and What We Can Do
The Rise of Cybersecurity Vulnerabilities: Why Data Breaches are on the Rise and What We Can Do
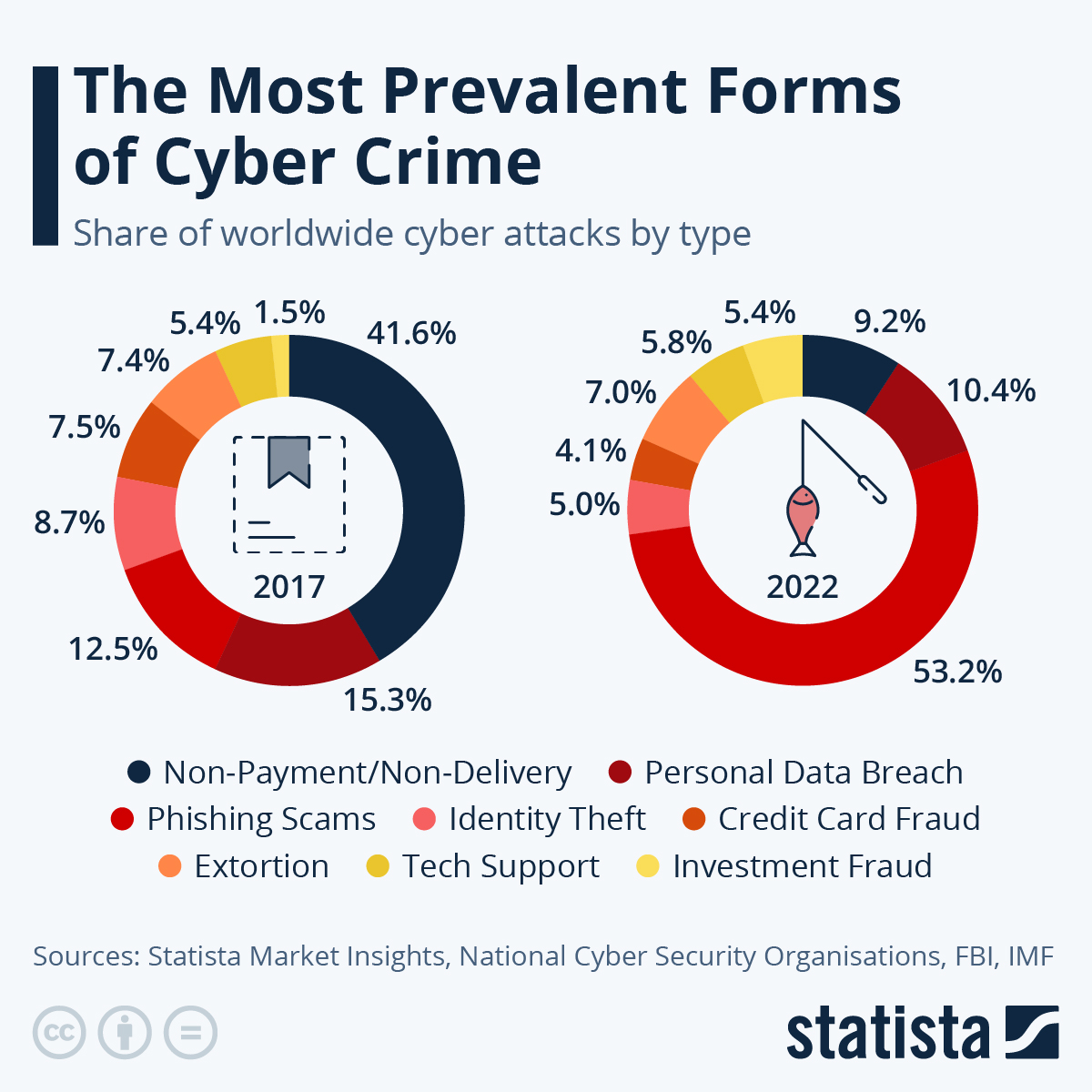
As the world becomes increasingly dependent on technology, cybersecurity vulnerabilities are becoming a growing concern for individuals, businesses, and governments. The frequency and severity of data breaches have been on the rise in recent years, with high-profile incidents affecting major corporations and organizations. According to a report by the Identity Theft Resource Center, the number of data breaches in the United States increased by 67% in 2020, with over 1,100 breaches affecting more than 155 million individuals. This alarming trend suggests that cybersecurity is no longer a luxury, but a necessity in today's digital age.
The rise of cyber threats can be attributed to several factors, including the increasing use of cloud computing, the Internet of Things (IoT), and the growing reliance on remote work, which has created more vulnerabilities for hackers to exploit. In addition, the lack of awareness and education among individuals and organizations about cybersecurity best practices has contributed to the surge in data breaches. As a result, it's essential to understand the causes, consequences, and prevention strategies to mitigate these threats.
Causes of Cybersecurity Vulnerabilities
The root causes of cybersecurity vulnerabilities can be broadly categorized into three main areas: human error, technology, and external threats.
Human Error
Human error is a significant contributor to cybersecurity vulnerabilities. This can include:
• Phishing attacks: Social engineering tactics used to trick individuals into divulging sensitive information. According to a report by Wombat Security, 92% of malware is spread through phishing.
• Password management: Weak or easily guessable passwords are a common vulnerability, with 63% of people using the same password across multiple sites.
• Ignoring software updates: Failing to update software, operating systems, and browser plugins can leave devices vulnerable to exploitation.
• Employee negligence: Lack of awareness and education among employees about cybersecurity best practices can lead to accidental mistakes.
Technology Vulnerabilities
Technology vulnerabilities arise from:
• Outdated software: Using outdated software or equipment can leave devices open to known vulnerabilities.
• Lack of encryption: Not using encryption to protect data can make it easily accessible to hackers.
• Unsecured networks: Unsecured Wi-Fi networks can be vulnerable to unauthorized access.
• Inadequate backups: Lack of regular backups can lead to data losses in the event of a breach.
External Threats
External threats come from:
• Hacking groups: Sophisticated hacking groups can gain access to sensitive information through various means, including phishing, social engineering, and exploiting vulnerabilities.
• State-sponsored hacking: Nation-state hacking groups can launch targeted attacks against organizations and individuals for financial or strategic gain.
• Insider threats: Authorized personnel can intentionally or unintentionally cause harm to an organization by accessing or mishandling sensitive information.
Consequences of Cybersecurity Vulnerabilities
The consequences of cybersecurity vulnerabilities can be severe and far-reaching.
• Financial loss: Data breaches can result in significant financial losses, with the average cost of a data breach being $3.86 million, according to a report by IBM.
• Reputation damage: A cyber attack can damage an organization's reputation, leading to loss of customer trust and loyalty.
• Legal and regulatory penalties: Failure to comply with data protection laws and regulations can result in significant fines and penalties.
• Loss of business operations: Cyber attacks can disrupt business operations, causing downtime and impacting productivity.
Prevention Strategies
To mitigate cybersecurity vulnerabilities, organizations and individuals can take the following measures:
Essential Security Measures
• Implement robust security protocols: Install security software, use firewalls, and update antivirus software regularly.
• Use strong passwords: Use complex passwords, change them frequently, and avoid using the same password across multiple sites.
• Conduct regular security audits: Regularly scan for vulnerabilities, update software, and patch known exploits.
Education and Awareness
• Educate employees: Provide regular training and awareness programs to educate employees about cybersecurity best practices.
• Promote best practices: Share cybersecurity best practices, such as phishing awareness, password management, and safe browsing habits.
• Stay informed: Stay up-to-date with the latest cybersecurity threats and best practices to remain proactive.
Conclusion
Cybersecurity vulnerabilities are a growing concern in today's digital age, with data breaches becoming more frequent and severe. Understanding the causes, consequences, and prevention strategies is crucial to mitigate these threats. By implementing essential security measures, educating employees, and staying informed, individuals and organizations can reduce their risk of falling victim to cyber attacks. As the threat landscape continues to evolve, it's essential to remain vigilant and proactive in the fight against cybersecurity vulnerabilities.
Key Takeaways
• The number of data breaches has increased significantly in recent years.
• Human error, technology vulnerabilities, and external threats are the primary causes of cybersecurity vulnerabilities.
• Financial loss, reputation damage, and legal and regulatory penalties are the consequences of cybersecurity vulnerabilities.
• Essential security measures, education, and awareness are key to preventing cybersecurity vulnerabilities.



Related Post

The Mysterious Death of Nate Bossi: What Really Happened?

Travis Scott Finally Confirms Net Worth Soaring To Impossible Heights In 2025 Firepower

Unlocking the Power of Amazon.com/Redeem: A Comprehensive Guide

The Mysterious Energy of the January 25 Zodiac: Unraveling the Secrets of Aquarius and Capricorn Connections.