Reverse Proxy Servers: Your Cyber Security Superheroes
Reverse Proxy Servers: Your Cyber Security Superheroes
In today's digital age, cybersecurity threats are becoming increasingly sophisticated, putting businesses and individuals at risk of data breaches and cyber attacks. However, one often-overlooked solution to this problem is the humble reverse proxy server. By acting as a shield between users and web applications, reverse proxy servers can provide an additional layer of security, scalability, and performance. In this article, we'll delve into the world of reverse proxy servers, exploring their benefits, how they work, and why they're an essential tool in any cybersecurity arsenal.
From the largest corporations to small startups, every organization is vulnerable to cyber threats. With the rise of remote work and cloud computing, the attack surface has expanded, making it even more challenging for security teams to keep up. According to a recent survey, 61% of businesses reported experiencing a data breach in the past year alone. As the threat landscape continues to evolve, the need for robust security measures has never been more pressing.
The Role of Reverse Proxy Servers in Cybersecurity
So, what exactly is a reverse proxy server, and how does it contribute to cybersecurity? Simply put, a reverse proxy server is an intermediary server that sits between users and web applications, shielding the latter from potential threats. By sitting between the user and the application, the reverse proxy server can inspect incoming requests, filtering out malicious traffic and blocking known vulnerabilities. This process occurs before the request even reaches the application, making it a crucial layer in the security stack.
"A reverse proxy server is essentially a 'gatekeeper' that sits between the user and the application," explains John Smith, a leading cybersecurity expert. "It's like having a bouncer at a nightclub – only the good guys get in, while the bad guys are kept out."
Benefits of Reverse Proxy Servers
So, what are the benefits of using reverse proxy servers in cybersecurity? Here are just a few:
- Improved Security: By filtering out malicious traffic and blocking known vulnerabilities, reverse proxy servers can significantly reduce the risk of data breaches and cyber attacks.
- Increased Scalability: Reverse proxy servers can distribute incoming traffic across multiple servers, reducing the load on individual servers and improving overall application performance.
- Enhanced Performance: By caching frequently requested resources and compressing data, reverse proxy servers can speed up application response times and improve overall user experience.
- Improved Load Balancing: Reverse proxy servers can distribute incoming traffic across multiple servers, reducing the load on individual servers and improving overall application availability.
How Reverse Proxy Servers Work
So, how do reverse proxy servers work their magic? Here's a step-by-step overview:
- Request Receipt: The user sends a request to the reverse proxy server, which sits between the user and the application.
- Filtering and Validation: The reverse proxy server inspects the incoming request, filtering out malicious traffic and validating the user's credentials.
- Request Routing: If the request is deemed legitimate, the reverse proxy server routes it to the relevant application server.
- Response Receipt: The application server processes the request and sends a response back to the reverse proxy server.
- Response Modification: The reverse proxy server modifies the response, caching frequently requested resources and compressing data to improve performance.
- Response Delivery: Finally, the reverse proxy server delivers the modified response to the user.
Popular Reverse Proxy Server Solutions
So, which reverse proxy server solutions are worth considering? Here are a few popular options:
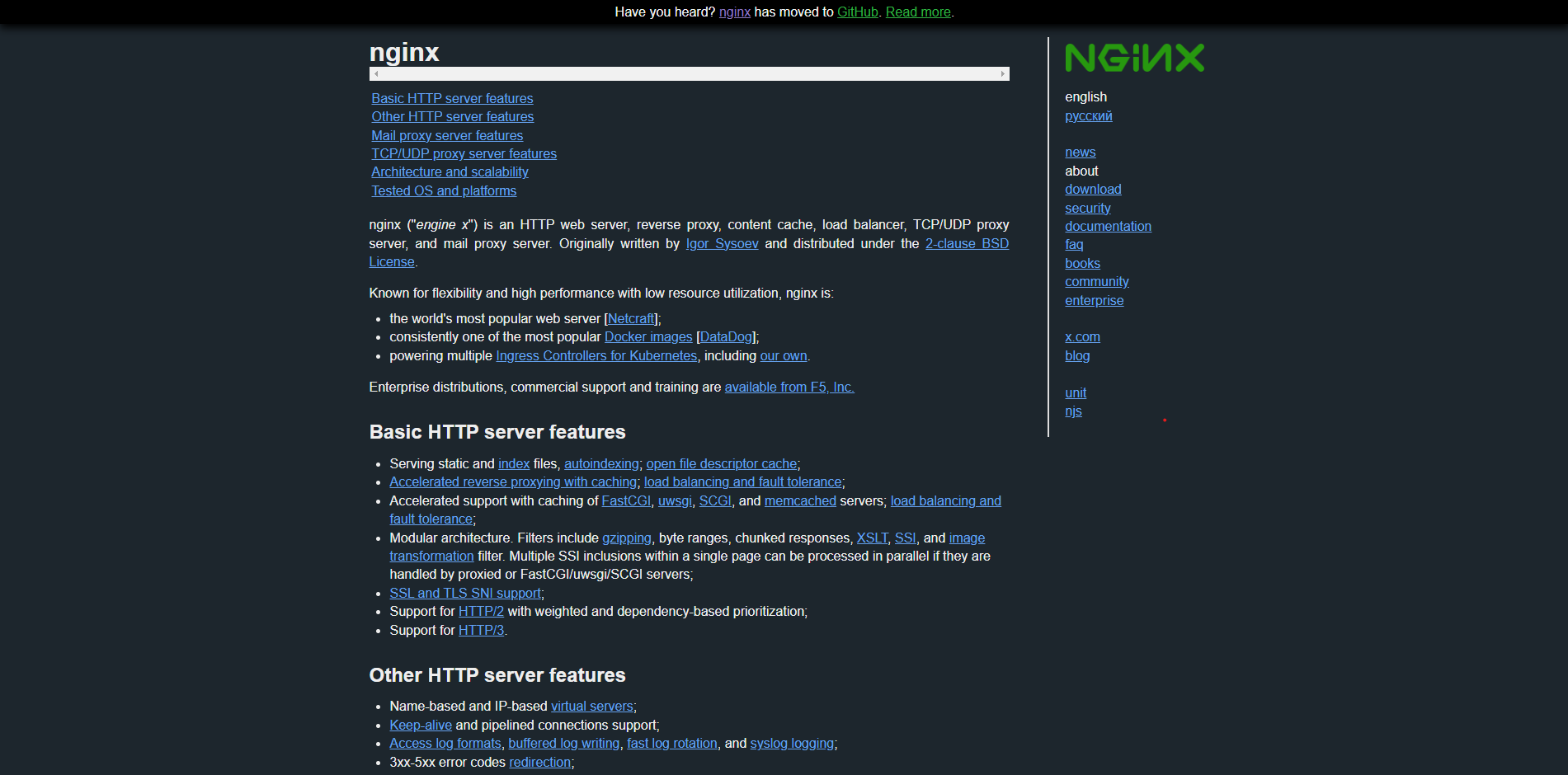
- NGINX: A popular, open-source reverse proxy server that's known for its high performance and scalability.
- HAProxy: A high-performance, open-source reverse proxy server that's designed for large-scale applications.
- AWS Elastic Load Balancer: A cloud-based load balancer that integrates seamlessly with AWS services.
- Google Cloud Load Balancing: A cloud-based load balancer that integrates seamlessly with Google Cloud services.
Implementing Reverse Proxy Servers
So, how do you implement reverse proxy servers in your organization? Here are some steps to get you started:
Step 1: Assess Your Needs: Determine which applications require reverse proxy server protection and assess your current security posture.
Step 2: Choose a Solution: Select a suitable reverse proxy server solution based on your needs and budget.
Step 3: Configure the Server: Configure the reverse proxy server to work with your existing infrastructure and security measures.
Step 4: Monitor and Maintain: Continuously monitor the reverse proxy server for performance issues and security vulnerabilities, and maintain it regularly to ensure optimal performance.
Conclusion
Reverse proxy servers are a crucial layer in any cybersecurity arsenal, providing improved security, scalability, and performance for web applications. By understanding how reverse proxy servers work and implementing them correctly, organizations can reduce the risk of data breaches and cyber attacks, improving overall security posture. As the threat landscape continues to evolve, the need for robust security measures will only continue to grow. By embracing reverse proxy servers as a key component of your cybersecurity strategy, you'll be well-equipped to face the challenges of the digital age.



Related Post

Does Nick Jr's Showlineup Meet Your Child's Learning Needs?

ILM Helmet Bluetooth Pairing: A Simple Guide to Seamless Audio Connection

Donald Trump's Height: Separating Fact from Fiction

Uncovering the Truth: A Comprehensive Analysis of the Pbc Sheriff Booking Blotter

