Cracking the Code: Understanding Internet Protocol Security (IPsec) to Safeguard Your Digital Life
Cracking the Code: Understanding Internet Protocol Security (IPsec) to Safeguard Your Digital Life
The internet has revolutionized the way we live, work, and communicate. With billions of people connected to the world through the internet, online security has become a top priority. In recent years, cyber threats and data breaches have plagued individuals and organizations alike, resulting in lose of sensitive information and financial losses. One crucial technology that has been instrumental in mitigating these threats is Internet Protocol Security (IPsec). In this article, we will delve into the world of IPsec and explore its importance, key components, and real-world applications.
IPsec is a suite of protocols designed to secure internet communications by encrypting and authenticating IP packets at the network and transport layers. Developed in the late 1990s, IPsec is a critical component of Internet Protocol Suite and provides confidentiality, integrity, and authenticity of data transmitted over IP networks.
Hans Scharnhorst, a leading IPsec expert at Cisco, explains that "IPsec is not just a security protocol, but a traffic control mechanism that allows for secure communication over the internet." He continues, "The primary goal of IPsec is to ensure that data is encrypted and authenticated, making it virtually impossible for unauthorized parties to intercept and read or modify the data."
The key components of IPsec include:
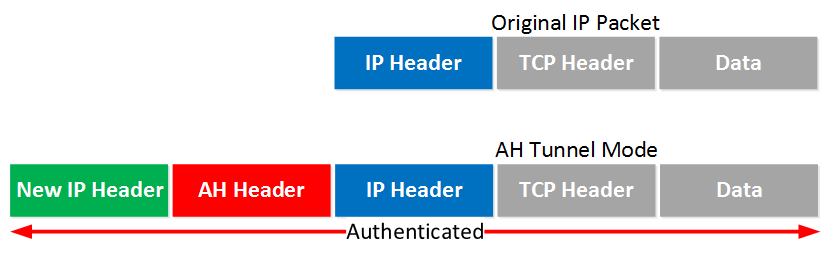
• **Authentication Header (AH) and Encapsulating Security Payload (ESP)**: These two components work together to provide confidentiality, integrity, and authenticity of data packets. AH ensures that the sender and receiver of the packet are verified, while ESP encrypts the payload, making it unreadable to any entities that intercept the packet.
• **Transport Mode and Tunnel Mode**: IPsec operates in two modes - transport mode and tunnel mode. Transport mode encrypts the payload of the packet, while tunnel mode encrypts the entire packet, including the header.
• **Key Exchange Protocols**: Key exchange protocols such as IKE (Internet Key Exchange) and IKEv2 (IKE version 2) are used to establish and manage the encryption keys between communicating parties.
The importance of IPsec cannot be overstated. According to a report by VPN Comparison, a staggering 80% of organizations use IPsec in their security protocols. This is because IPsec:
• **Prevents Eavesdropping and Interception**: IPsec ensures that data transmitted over the internet is encrypted, making it virtually impossible for unauthorized parties to intercept and read the data.
• **Protects Against Denial of Service (DoS) and Distributed Denial of Service (DDoS) Attacks**: IPsec prevents DoS and DDoS attacks by authenticating the sender of IP packets and filtering out unauthorized traffic.
• **Meets Compliance Requirements**: Many organizations are required to comply with data protection regulations such as HIPAA (Health Insurance Portability and Accountability Act) and PCI-DSS (Payment Card Industry Data Security Standard). IPsec helps organizations meet these compliance requirements.
Real-world applications of IPsec include:
• **Secure Remote Access**: IPsec is widely used to secure remote access to organizational networks, ensuring that remote workers and partners can access resources securely.
• **Virtual Private Network (VPN)**: Many VPNs use IPsec to provide a secure and private connection between two points over the internet.
• **Software-defined Networking (SDN)**: IPsec is used in SDN to ensure secure communication between components of the SDN architecture.
However, IPsec is not without its challenges. The main obstacle is the complexity of implementing and managing IPsec. According to an article by TechTarget, "IPsec is notoriously difficult toconfigure and manage, especially for large-scale networks."
IPsec also poses scalability challenges as it requires significant computational resources to encrypt and decrypt packets in real-time. A study by RSA Security highlighted that IPsec can result in reduced network performance, making it a significant investment for organizations with high-bandwidth applications.
In conclusion, IPsec is an essential technology in ensuring secure communication over the internet. While there are challenges associated with implementing and managing IPsec, the benefits far outweigh the costs. As IPsec expert, Espen Carlsen, advises "IPsec should be considered a single point of security across the entire network, rather than a separate solution to specific security threats."


Related Post

Unveiling The Allure Of Camilla Araujo: The OnlyFans Video Sensation

Meet the Behind-the-Scenes Moms Who Make Gabbriette Bechtel Shine!

Discover the Hidden Gem of Southeast Asia: Dili, the Unassuming Capital of East Timor

Unlocking the Truth: A Guide to Lexington County South Carolina Inmate Search

